Introduction to PCIe Access Control Services
- Access Control Services(ACS)
- Address Translation Service(ATS)
1. Background
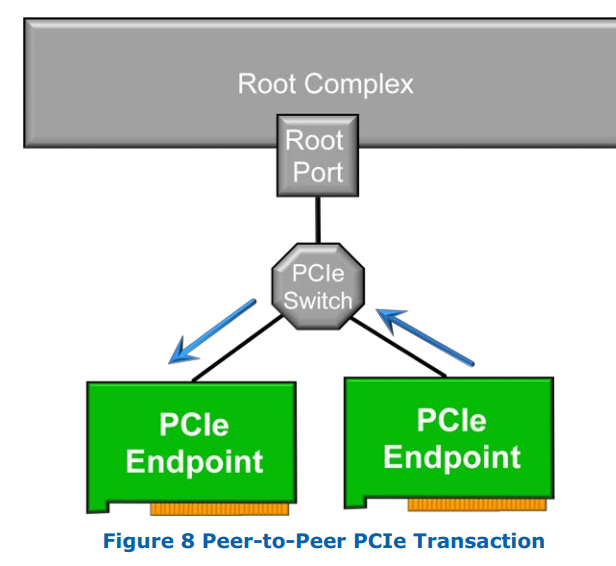
The PCIe specification allows for peer-to-peer transactions. This means that it is possible and even desirable in some cases for one PCIe endpoint (say a Virtual Function – or even a standard PCIe Function) to send data directly to another endpoint without having to go through the Root Complex.
2. What is ACS
2.1 disbale Peer-to-Peer PCIe transaction
Access Control Services (ACS) provides a mechanism by which a Peer-to-Peer PCIe transaction can be forced to go up through the PCIe Root Complex. ACS can be thought of as a kind of gate-keeper —preventing unauthorized transactions from occurring.
Without ACS, it is possible for a PCIe Endpoint to either accidentally or intentionally (maliciously) write to an invalid/illegal area on a peer endpoint, potentially causing problems.
2.2 disbale ATS
By using ATS , any device can claim it’s using an address that’s already been translated, and thus bypass IOMMU translation. For trusted devices, this is a useful performance improvement. For untrusted devices, this is a big security threat. ATS could allow a compromised device to ignore the IOMMU and write to places it shouldn’t have access to.
Luckily, there’s an ACS setting that can disable ATS for any given device.
参考资料: