VT-d Interrupt Remapping
本文将介绍VT-d Interrupt Remapping的motivation,然后推荐一篇介绍Interrupt Remapping细节的文章,最后以一个具体的例子来展示VT-d Interrupt Remapping的用法。
motivation
- Supporting isolation and routing of interrupts from devices and external interrupt controllers to appropriate VMs.
- Supporting x2APIC
details
可以详细阅读此文。
https://kernelgo.org/interrupt-remapping.html
demo usage
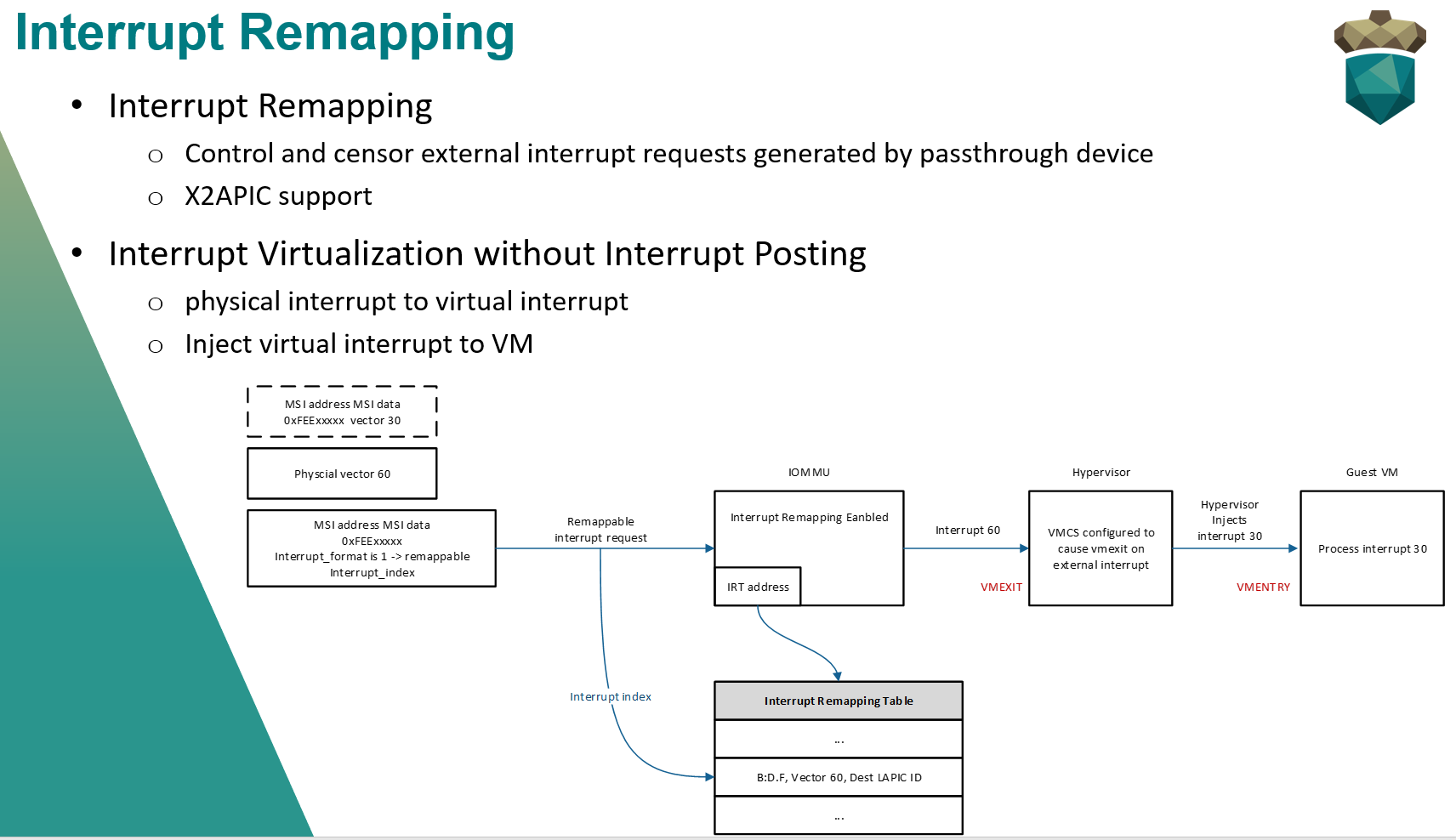
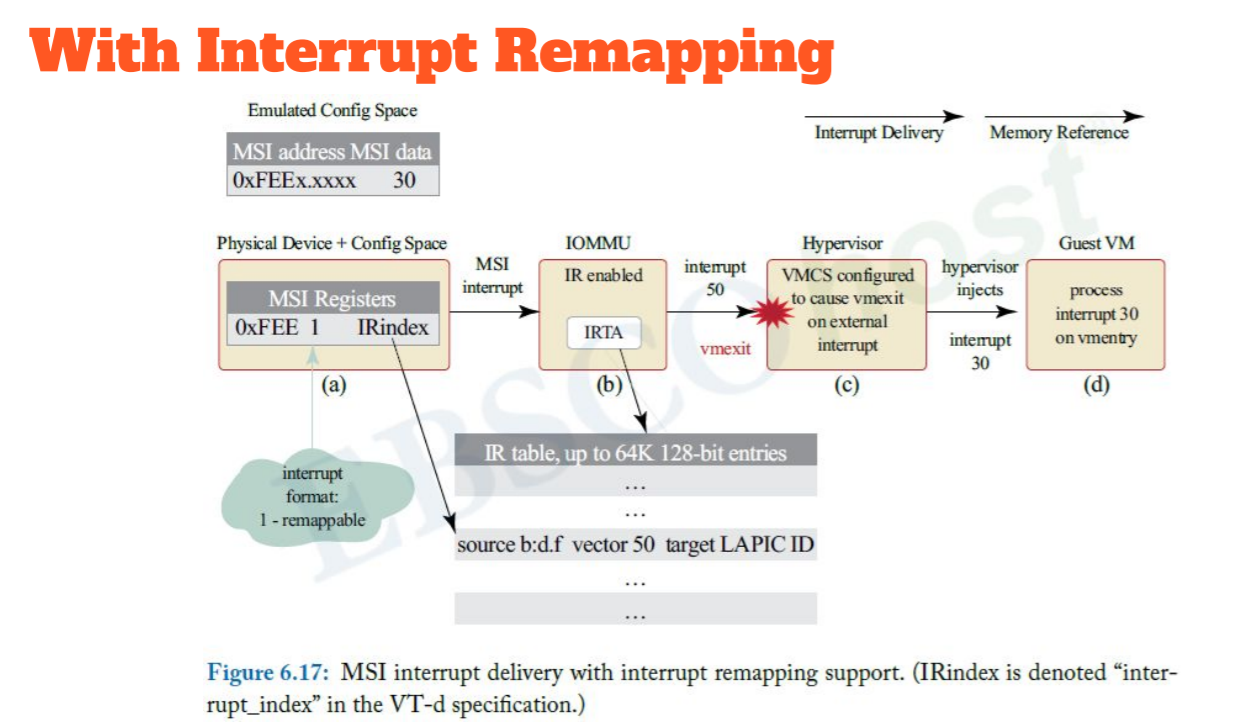
以上图为例,将展示VT-d Interrupt Remapping的具体过程。
- 当guest配置MSI address和MSI data时,hypervisor(hv)会trap,解析相关field,得到virtual interrupt的vector为30,而对应的physical interrupt的vector为60。这样hv会记录physical interrupt到virtual interrupt的映射(vector 60 -> vector 30)。
- 分配一个IRTE并且按照IRTE的格式要求填好IRTE的每个属性。如:B:D.F, Vector(60), 运行目标vCPU的物理CPU的LAPIC ID。
- 按照Remapping format的格式对MSI进行编程。如:将Interrupt Format置1,设置中断的interrupt_index。
- 设置VMCS(configured to cause vmexit on external interrupt)。当物理CPU收到vector为60的中断时,会发生VM-Exit。
- hv处理VM-Exit,根据physical interrupt到virtual interrupt的映射(vector 60 -> vector 30)关系,为guest注入vector为30的interrupt。
- VM-Entry到guest VM,process vector为30的interrupt。
rethinking the motivation
两者可以完成相同的功能。那么为什么还要有VT-d Interrupt Remapping呢?
在Following the White Rabbit:Software attacks against Intel(R) VT-d technology一文中找到了答案:vulnerable to the BDF spoofing attack。
Even though the interrupt remapping seems vulnerable to the BDF spoofing attack (just like DMA
remapping is), still we believe it has a potential to prevent all the above-mentioned MSI attacks, because we anticipate that none of the interrupt vector used in our attacks should be allowed to any devices in the system. In that case, BDF spoofing would not bring any advantage to the attacker, as there should be no device at all that the attacker might want to impersonate, which could deliver those dangerous interrupts, such as SIPI, syscall interrupts, or the #AC exception.
BDF spoofing is a type of a hardware attack against VT-d, where a malicious device generates PCIe packets with spoofed BDF address.
说白了,VT-d Interrupt Remapping可以解决security问题。
参考资料: